
Challenges in Implementing Digital Identities in the Industrial IoT
Challenges in Implementing Digital Identities in the Industrial IoT
Challenges in Implementing Digital Identities in the Industrial IoT

Why Implementation in the Industrial IoT Is Particularly Challenging
Challenge 1: Building and operating a PKI in the industrial IoT
For a device to have a trustworthy digital identity, it needs a digital certificate.
This certificate is issued by a Public Key Infrastructure (PKI), the central trust authority in the Industrial IoT.
In practice, this includes:
Building a scalable certification infrastructure
Integrating it into existing systems and processes
Ensuring availability and trust
The effort rarely lies in the PKI itself, but in embedding it into existing workflows.
Responsibilities for issuing, renewing, and monitoring certificates are often unclear — and this is where operational gaps emerge.
This leads to increased coordination between IT and OT and raises the risk of misconfigurations during operation.
Challenge 2: Certificate rollout and distribution
The biggest hurdle often arises at the very first step: How does the digital identity get onto the device?
In many industrial environments, automated processes are missing.
As a result, certificates have to be uploaded to devices manually.
Each device must be configured individually
The process is time-consuming and error-prone
Scaling across many devices becomes difficult
Certificates are installed one by one — a process that can take days or even weeks in larger deployments with hundreds of devices.
In typical projects, this step alone can significantly delay rollout, especially when production downtime must be avoided.
For many industrial components, such as sensors or PLCs, the technical foundation for automation is simply not in place.
Challenge 3: Heterogeneous systems and lack of standardization
A machine running an outdated Linux version
Another using a proprietary system
A third based on Windows
Challenge 4: Operation and lifecycle management
Continuously checking certificate validity
Detecting and revoking compromised devices quickly
Maintaining full traceability of changes and processes
How these challenges reinforce each other
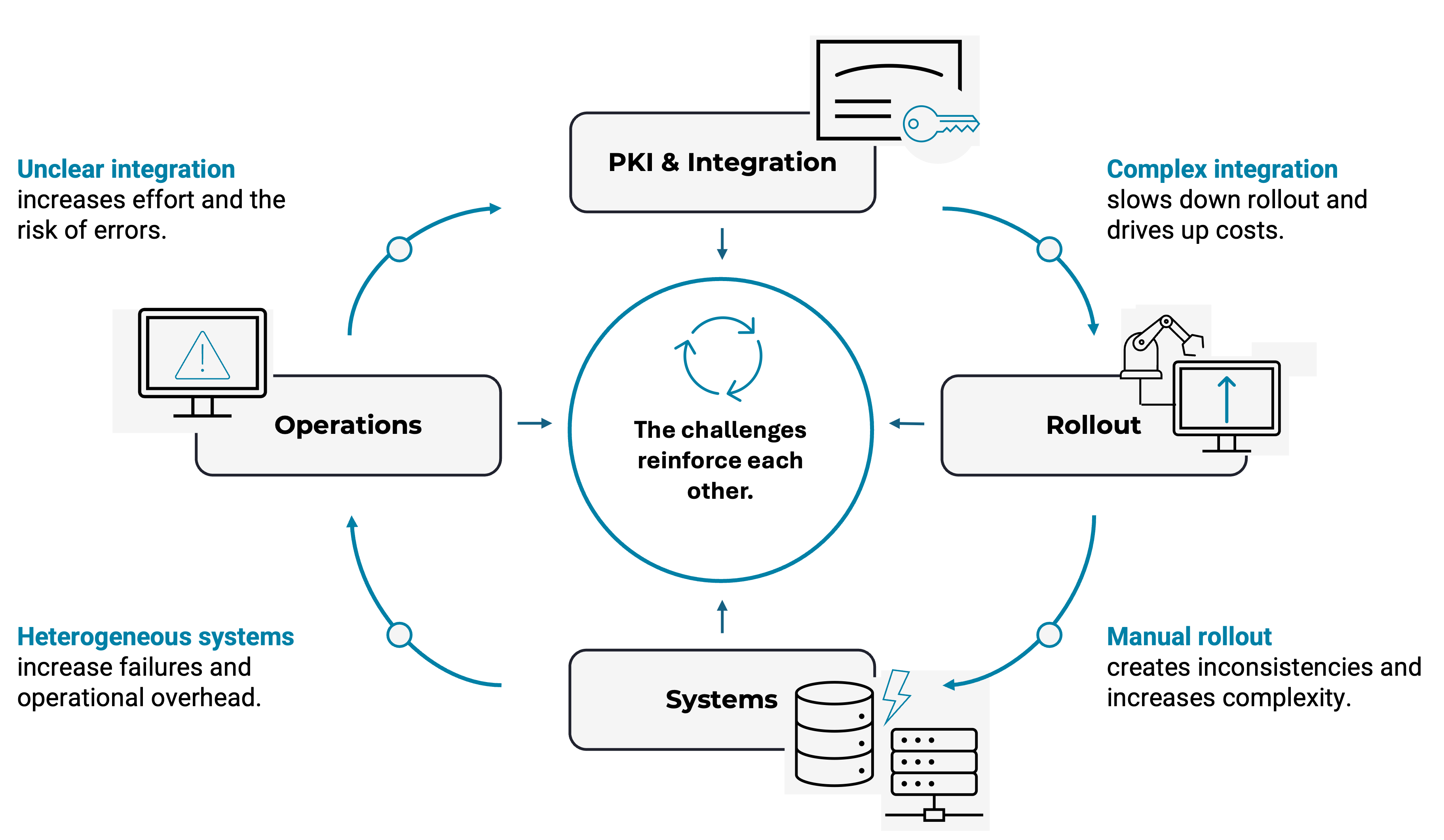
High time expenditure
Slow implementation
Increasing risks
What is required for successful implementation
Automated processes for deploying and renewing certificates
Clearly defined responsibilities for issuance, operation, and monitoring
Integration that works with existing systems and heterogeneous environments
Solutions that do not require individual customization for each device
Conclusion
- Why implementation in the industrial IoT is particularly challenging
- Challenge 1: Building and operating a PKI in the industrial IoT
- Challenge 2: Certificate rollout and distribution
- Challenge 3: Heterogeneous systems and lack of standardization
- Challenge 4: Operation and lifecycle management
- How these challenges reinforce each other
- What is required for successful implementation
- Conclusion