
Stay up to date.
Discover the latest IT security challenges and essential measures needed to protect your business.

Industrial security for OT and IoT
More devices are connected to the Internet of Things (IoT) than there are people on Earth. Many of these devices are used in critical industries, making them increasingly attractive targets for cyberattacks.
To mitigate these risks, security by design must be implemented from the outset. By integrating IT security into the manufacturing process and across the entire value chain, devices can be secured early and vulnerabilities significantly reduced.
Public key infrastructures (PKI) and key management systems are essential in this context. Digital identities and encrypted certificates ensure device integrity and enable secure authentication of sensors, devices, and platforms.
This allows trusted devices to be identified while preventing unauthorized access. At the same time, encrypted communication protects the confidentiality and integrity of transmitted data.
Protect your business with DEVITY and future-proof your devices, production systems, and processes.
Cybersecurity at the turn of the era
Digital identities: Basic requirement for protection against cyberattacks
Published on 24. Nov. 2023 I Maschinenmarkt
Gain insights into:
The challenges of industrial IoT.
What are digital identities?
Why do digital identities form the basis of IT security?
How do digital identities establish trust within the value chain?
Why digital identities are a crucial element of security by design?
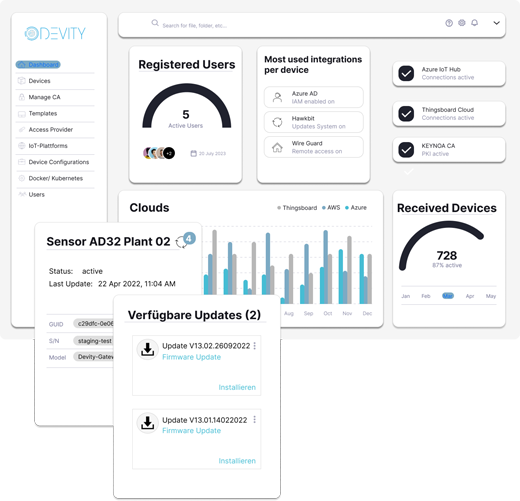
Securing the Internet of Things with KEYNOA
Integrate many IoT devices quickly and securely
Published on 01 Sep. 2023 I IT&Production
Our guest article covers:
How has the provisioning process worked so far?
What role do manufacturer certificates play in ensuring security?
How can IoT devices be securely integrated using an automated process?
How can device manufacturers secure digital identities using hardware?
How can the remote operation of IoT devices be ensured?
IT security at the core of the digital product lifecycle
Preparing components for the digital age
Published on 01 Feb. 2023 I SPS Magazine
Gain technical background knowledge on the topic of security by design:
What is Security by Design?
What standards does the IEC 62443 standard entail?
How can a device's identity be secured?
How can IoT devices be securely authenticated for deployment?
Presentation of a flexible solution for securely configuring devices.
5 questions for... Sven Uthe Managing Director and CTO of DEVITY
Published on Jan. 2023 I Industrial Automation
Gain an understanding of digital identities:
What are digital identities?
What opportunities do digital identities offer?
Why should manufacturers act urgently?
What should device manufacturers keep in mind?
How can configuration processes be made more efficient?
Secure provisioning of components on any data platform.
Published on Feb. 2021 I VDMA
Gain technical background knowledge on the topic of security by design:
Challenges of installing and configuring IoT devices.
Secure onboarding processes for IoT devices.
The significance of IEC 62443 for the industry.
Meet compliance for digital value creation today!
Protect your company from cyber threats by leveraging digital identities and securing your industrial components.
More on the topic of IT security
Get in touch.
Would you like to book a demo or have further questions? Schedule a session with our CEO to learn how DEVITY enhances the security and scalability of infrastructures and projects.











